In an age where our lives are increasingly intertwined with the digital world, the need for robust security and verifiable trust has never been more critical. Every click, every transaction, every message sent across the internet relies on a sophisticated invisible framework designed to protect our data and ensure our interactions are authentic. At the very heart of this framework lies a concept that is both elegant and profoundly powerful: the public key. Far from being a niche technical term, understanding the public key is key to comprehending how modern digital security, from secure websites to cryptocurrencies, truly functions.
The Foundation of Digital Trust: What is a Public Key?
A public key is one half of a cryptographic key pair, a fundamental component of asymmetric cryptography. Unlike symmetric cryptography, where the same key is used for both encryption and decryption, asymmetric cryptography employs two mathematically linked but distinct keys: a public key and a private key. This ingenious design allows for a revolutionary approach to secure communication and authentication.
Unpacking the Asymmetric Pair
Imagine a digital mailbox. This mailbox has a slot through which anyone can drop a letter (your public key), but only you possess the unique key to open the mailbox and read its contents (your private key). This analogy perfectly encapsulates the core principle:
- Public Key: This key can be freely shared with anyone. It’s used by others to encrypt messages intended for you or to verify digital signatures that you have created.
- Private Key: This key must be kept absolutely secret and secure. It’s used by you to decrypt messages encrypted with your public key or to create digital signatures.
The mathematical relationship between these keys is such that while they are interdependent, it is computationally infeasible to derive the private key from the public key alone. This one-way computational hardness is the bedrock of its security.
Characteristics of Public Keys
Public keys are typically long strings of alphanumeric characters, mathematically derived from the private key. Their design incorporates several crucial characteristics:
- Computational Link: They are inextricably linked to their private counterpart through complex mathematical algorithms (e.g., RSA, Elliptic Curve Cryptography).
- Non-Reversibility: It is practically impossible to reverse-engineer the private key from the public key, even with immense computing power.
- Open Distribution: Public keys are designed to be distributed widely, enabling anyone to initiate secure communication or authenticate identities.
Actionable Takeaway: Recognize that while a public key can be openly shared, its associated private key demands the highest level of secrecy. Never expose your private key.
How Public Key Cryptography Works: Encryption & Authentication
The power of public keys manifests in two primary functions: enabling confidential communication through encryption and verifying identity and integrity through digital signatures.
Secure Communication: Encryption with Public Keys
When you want to send sensitive information, like your credit card details on an e-commerce site, public key encryption ensures only the intended recipient can read it. Here’s how it generally works:
- Key Exchange: Alice wants to send a secure message to Bob. Bob shares his public key with Alice.
- Encryption: Alice uses Bob’s public key to encrypt her message.
- Transmission: The encrypted message is sent across an insecure channel (like the internet).
- Decryption: Only Bob, possessing the corresponding private key, can decrypt the message and read its original content.
This process guarantees confidentiality, meaning that even if an eavesdropper intercepts the encrypted message, they cannot decipher it without Bob’s private key. A practical example is sending an encrypted email, where the sender uses the recipient’s public key to encrypt the message, and only the recipient can unlock it.
Verifying Identity: Digital Signatures with Public Keys
Beyond confidentiality, public keys also enable authentication and integrity verification through digital signatures. This is crucial for proving who sent a message and that it hasn’t been altered.
- Hashing: The sender (Bob) generates a unique “fingerprint” (a hash) of his message.
- Signing: Bob then uses his private key to encrypt this hash, creating a digital signature.
- Attaching: Bob sends the original message along with his digital signature to Alice.
- Verification: Alice receives the message and signature. She generates her own hash of the received message. She then uses Bob’s public key to decrypt the received digital signature, revealing Bob’s original hash.
- Comparison: If Alice’s newly generated hash matches the hash decrypted from Bob’s signature, she can be confident that the message came from Bob (authentication) and has not been tampered with (integrity).
This mechanism provides non-repudiation – Bob cannot later deny sending the message. This is vital in legal contracts, software distribution, and financial transactions.
Actionable Takeaway: Understand that public keys serve two distinct but complementary roles: encrypting data for privacy and signing data for authenticity and integrity. These roles are often leveraged together for comprehensive security.
Real-World Applications: Where Public Keys Shine
Public keys are not just theoretical concepts; they are the unseen guardians of our digital world, underpinning many of the technologies we use daily.
Securing the Web: SSL/TLS
Every time you see “HTTPS” in your browser’s address bar and a padlock icon, you are witnessing public key cryptography in action. The Secure Sockets Layer (SSL) and its successor, Transport Layer Security (TLS), protocols use public keys to establish secure communication channels between your browser and websites.
- Website Identity: When you connect to a website, your browser requests its SSL/TLS certificate. This certificate contains the website’s public key and is digitally signed by a trusted Certificate Authority (CA).
- Trust Verification: Your browser uses the CA’s public key (pre-installed in your browser’s trust store) to verify the website’s certificate and, by extension, its public key. If valid, your browser trusts that it’s connecting to the legitimate website.
- Session Key Exchange: The website’s public key is then used to securely exchange a symmetric “session key” which encrypts all subsequent data transfer during that browsing session, ensuring both confidentiality and integrity.
Estimates suggest that over 80% of all web traffic is now encrypted with HTTPS, a testament to the critical role of public keys in securing online interactions.
Encrypted Email and Messaging
For individuals and organizations needing truly private communications, technologies like PGP (Pretty Good Privacy) and GPG (GNU Privacy Guard) leverage public keys for end-to-end email encryption.
- Key Exchange: Users exchange their public keys directly or via public key servers.
- Encryption & Signing: When Alice sends an email, she uses Bob’s public key to encrypt the message and her own private key to digitally sign it.
- Decryption & Verification: Bob receives the email, uses his private key to decrypt it, and Alice’s public key to verify her signature.
This ensures that only the intended recipient can read the message and that it genuinely originated from the sender.
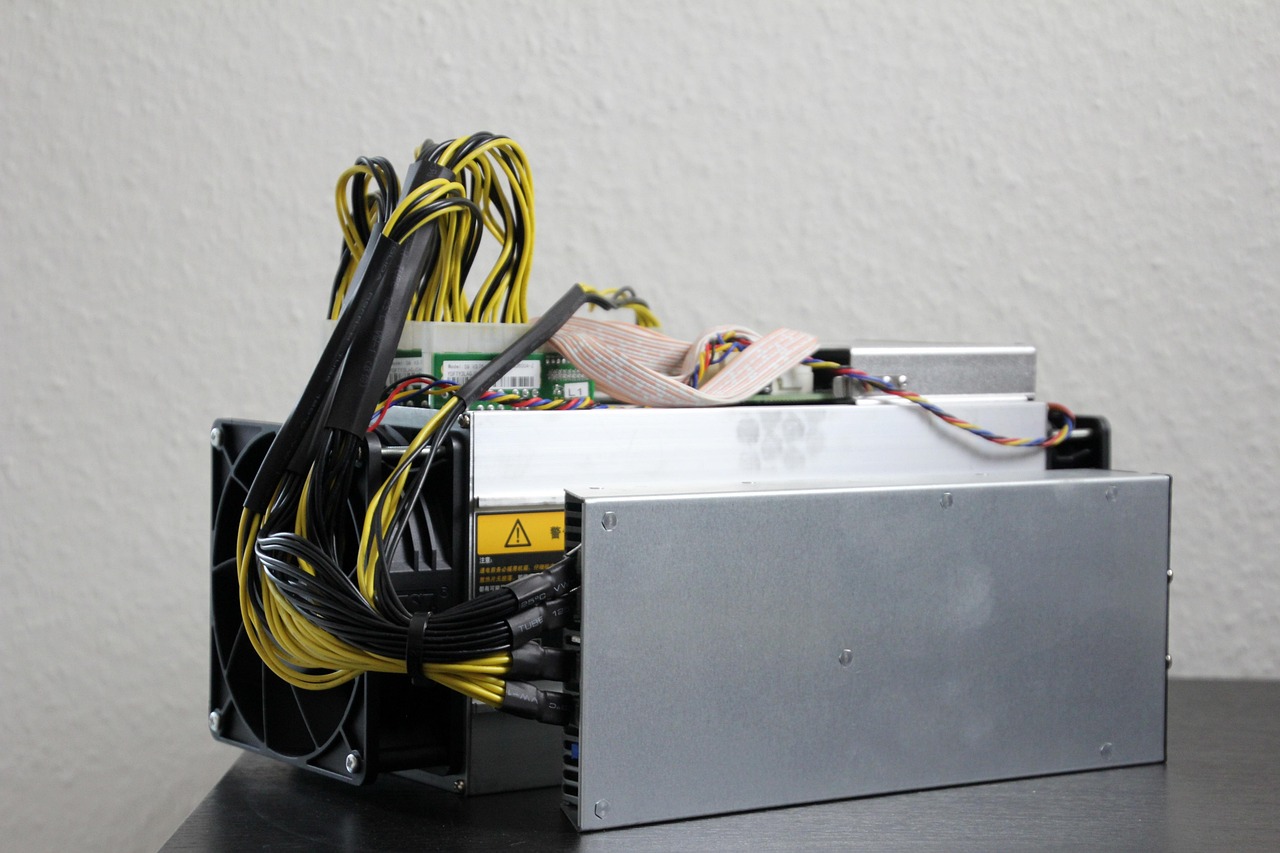
The Backbone of Cryptocurrencies
Public keys are foundational to the security and operation of cryptocurrencies like Bitcoin and Ethereum.
- Wallet Addresses: Your cryptocurrency “wallet address” is typically derived from your public key. This is the address you share for others to send you funds.
- Transaction Authorization: To spend or transfer cryptocurrency, you use your private key to digitally sign the transaction. This signature proves you are the legitimate owner of the funds without revealing your private key directly.
- Immutability: Once a transaction is signed and broadcast to the blockchain, its validity is verified using your public key, and it becomes an immutable part of the ledger.
Actionable Takeaway: Whenever you interact with an “HTTPS” website, send an encrypted message, or manage cryptocurrency, remember that public keys are silently working to secure your data and verify identities. Always ensure you are on a trusted HTTPS connection before sharing sensitive information.
Building Trust: Public Key Infrastructure (PKI)
While public keys are powerful, their utility hinges on a critical question: how do you know a public key genuinely belongs to the person or entity it claims to represent? This is where Public Key Infrastructure (PKI) comes into play, providing a framework for managing and authenticating public keys.
The Role of Certificate Authorities (CAs)
PKI establishes trust through a hierarchical system, with Certificate Authorities (CAs) at its core. CAs are trusted third parties responsible for issuing and managing digital certificates.
- Identity Verification: When a website or individual wants an SSL/TLS certificate, they apply to a CA. The CA rigorously verifies their identity.
- Certificate Issuance: Once verified, the CA issues a digital certificate, which essentially binds the applicant’s public key to their verified identity (e.g., domain name, organization name). This certificate is then digitally signed by the CA using its own private key.
- Trust Chain: Browsers and operating systems have a built-in list of trusted root CAs. When your browser encounters a website’s certificate, it traces the “chain of trust” back to one of these pre-approved root CAs to confirm its legitimacy.
Without CAs, establishing trust online would be a chaotic and vulnerable process, as anyone could claim to be Google or your bank.
Understanding Digital Certificates
A digital certificate is more than just a public key; it’s a digital identity document. It typically contains:
- The public key of the certificate holder.
- Information about the holder (e.g., domain name, organization, individual).
- Information about the issuer (the CA).
- The period of validity for the certificate.
- A digital signature of the issuing CA, guaranteeing its authenticity.
When your browser checks an SSL certificate, it first validates the CA’s signature on the certificate. If that signature is valid, it then trusts the public key contained within the certificate to be genuinely associated with the website you are visiting.
Actionable Takeaway: A digital certificate is the trust anchor that links a public key to a verified identity. Always pay attention to certificate warnings in your browser, as they indicate a potential breakdown in this trust chain.
Safeguarding Your Digital Life: Managing Public Keys
While public keys are meant to be openly distributed, their effective and secure management, along with the absolute secrecy of their private counterparts, is paramount for maintaining digital security.
Public Key Best Practices
Managing public keys effectively involves a few key considerations:
- Source Verification: Always verify the source of any public key you intend to use for encryption. If you’re encrypting an email for a contact, ensure you have their legitimate public key, not one an attacker might have substituted.
- Public Key Servers: For applications like PGP, public key servers act as directories where users can upload and retrieve public keys. While convenient, always cross-reference and confirm with the key owner if possible.
- Revocation: If a private key associated with a public key is ever compromised, it’s crucial to revoke the corresponding public key and certificate immediately. Certificate Revocation Lists (CRLs) and Online Certificate Status Protocol (OCSP) are mechanisms used by PKI to inform browsers and applications that a certificate is no longer valid.
The Imperative of Private Key Security
While public keys are designed for sharing, the private key is the crown jewel of your digital identity and security. Its compromise can lead to devastating consequences, including identity theft, financial loss, or unauthorized access to sensitive data.
Best practices for private key security include:
- Strong Passphrases: Always protect your private keys (especially software-based ones) with strong, unique passphrases or passwords.
- Hardware Security Modules (HSMs): For critical applications and high-value private keys (e.g., for CAs or cryptocurrency exchanges), hardware security modules offer dedicated, tamper-resistant hardware for storing and using private keys.
- Cold Storage: For highly sensitive private keys (e.g., for significant cryptocurrency holdings), “cold storage” (offline storage on devices disconnected from the internet) is often recommended.
- Regular Audits: For organizations, regular audits of private key management practices are essential to ensure compliance and detect vulnerabilities.
Actionable Takeaway: Treat your private key with the utmost care, protecting it more diligently than any physical key or document. If you suspect a private key has been compromised, act swiftly to revoke associated public keys and certificates.
Conclusion
The public key, and the asymmetric cryptography it enables, stands as a monumental achievement in computer science and the foundation of modern digital trust. From encrypting your web browsing sessions and securing your email to authenticating software updates and powering decentralized cryptocurrencies, public keys are indispensable. They empower us to communicate confidentially, verify identities reliably, and engage in secure transactions across a global, often untrusted network. As our digital lives continue to expand, understanding the elegant simplicity and profound impact of public keys will only become more vital, equipping us to navigate the complexities of the digital age with greater awareness and confidence.